Securing your security cameras
TL;DR My security cameras were sending video to China. The following is how I found out and stopped it.
A while back I bought some Power-over-Ethernet (PoE) security cameras and a Network Video Recorder (NVR). The setup was pretty easy - plug the cameras into the NVR, install the app on my phone, and link them up by either scanning the camera-specific QR codes, or hand-typing the codes as shown on the NVR monitor. Any system like this has to be plug & play for Joe Consumer to use, and it was. A few minutes worth of setup and I was all set.
A day or two later, I opened the app while at work to show a coworker, and that’s when it hit me: I didn’t open up any firewall ports, or anything on my network, yet I was watching live video streaming from my cameras. At this point, I just turned around staring at my phone thinking…
Huh, weird. How is this even working? Wait, what the hell - I didn’t even open up a firewall port. Is my firewall disabled? [while panic-running away] shit, shit, shit…*
I went home, fired up Wireshark, and captured packets with a source address of 192.168.1.180 - the IP address of my NVR. There were only a few destination IP addresses, and one stood out as the obvious recipient of my live-streaming video. A traceroute on that IP showed traffic routing to China hitting Amazon Web Services (AWS).
This made perfect sense - The cameras upload data to AWS and the mobile app hits a public endpoint to retrieve the data. Joe Consumer can use this without touching a router.
Okay, so now that I knew how it worked, I needed to change it. I run an Ubiquiti EdgeRouter-X, but any router worth a damn work (i.e. gives you fine-grained controls over the firewall) will work. I decided to drop all unnecessary traffic, leaving only a handful of things in place. Here’s a screenshot of my camera policy:
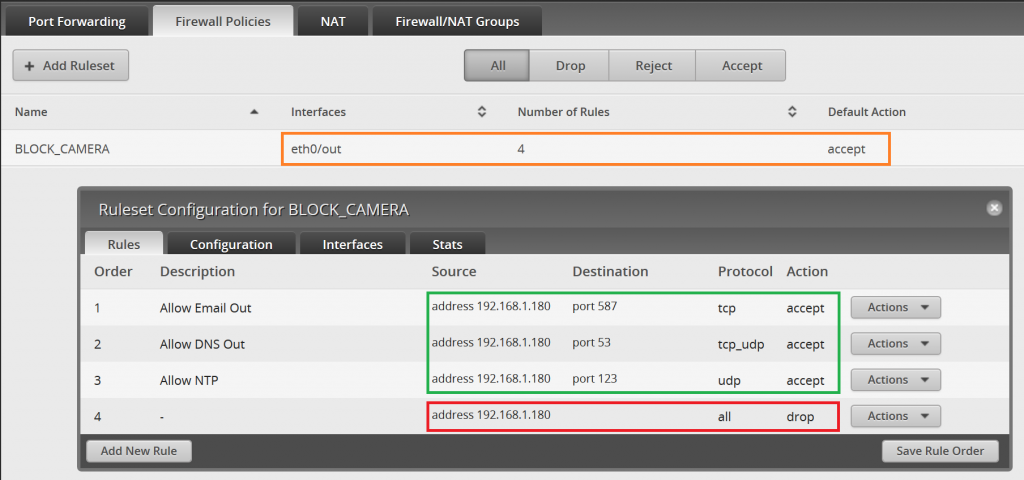
Outlined in orange, you’ll see the that I’ve specified eth0 as the Interface - that’s the one connected to my ISP. I set the Default (outbound) Action to “accept” because I don’t want to block outbound traffic for everything on my network. (Note that this is just one policy; there may be several other policies here)
I created 4 rules for this policy, all using my NVR’s IP address as the source. Outlined in green, you’ll see the services I’ve whitelisted & outlined in red you’ll see that all other traffic originating from the NVR is dropped. Email/DNS/NTP are all nice-to-haves and the system would function just fine without them.
So…everything’s locked down - how do I remotely view video? I have the ER-X configured as an OpenVPN server (a topic on its own) so I start a VPN connection from my phone before opening the app. It’s one extra step, but it’s well worth it. One (positive) unintended consequence to all this - the video lag time decreased significantly since my packets weren’t traveling to the other side of the world and back :)
*The world will be a safer place when Joe Consumer starts to think like this. Also, shame on me for not thinking like this before I plugged in all the things.